Anti-Cheat in Rust — How EAC Catches Cheaters and Why Not All of Them
What Is EAC and Why It Matters
Rust has been running Easy Anti-Cheat (EAC) from Epic Games since 2016. It launches alongside the game and operates at the Windows kernel level — it can see processes, drivers, and memory. A regular program never gets that kind of access, but EAC does.
EAC hunts for software that tampers with the game process: reading memory, injecting code, replacing textures, hooking system calls. If it finds something suspicious, it sends the data to its servers. The ban doesn't come instantly — sometimes it takes hours or even days.
Detection Methods — How EAC Finds Cheats
Signature analysis is the most basic method. EAC stores a database of "fingerprints" for known cheats: file hashes, code patterns in memory, characteristic process names. If software hits this database, it gets detected on the next scan. Public cheats land in the database fast; private ones take significantly longer due to fewer users.
Behavioral analysis tracks anomalies in gameplay. If a player consistently lands headshots at extreme distances or their crosshair snaps between targets — that's a behavioral marker. The system doesn't ban immediately but flags the account for manual review.
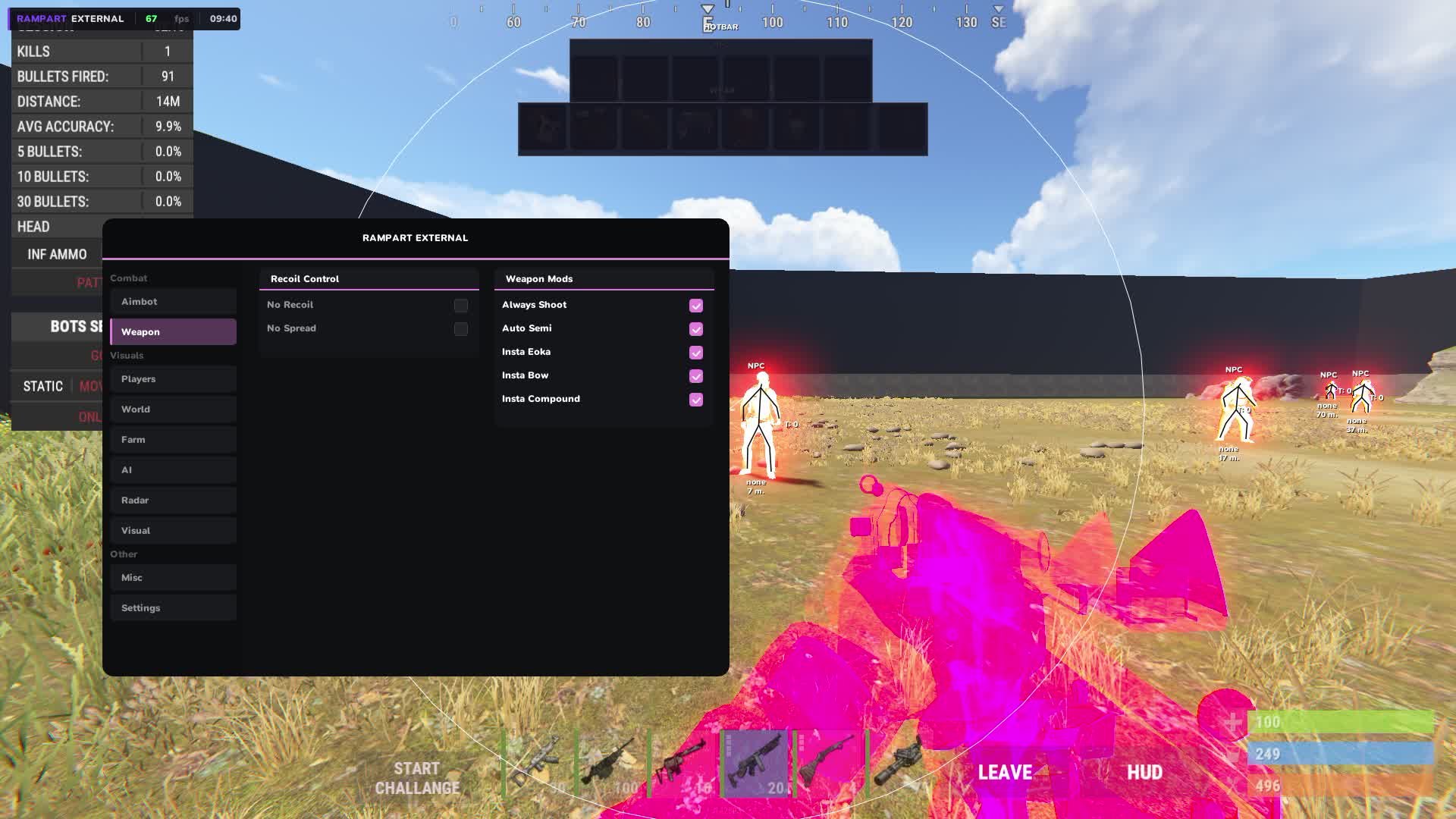
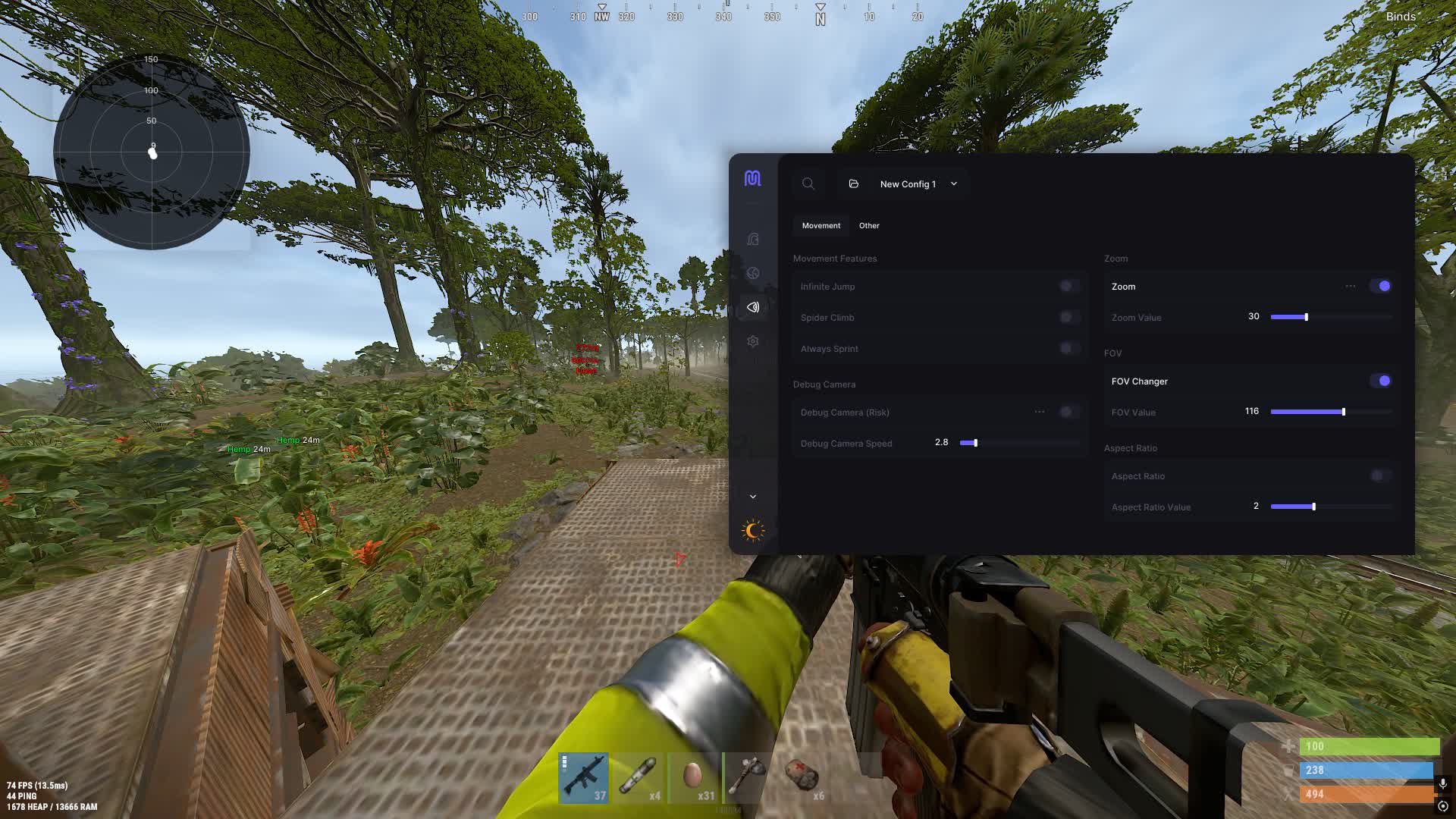
Memory analysis — EAC periodically scans the game process RAM. It looks for injected code, suspicious modules, and modified data structures. External cheats that run outside the game process are harder to catch with this method.
HWID tracking — EAC collects hardware identifiers from your PC and ties them to your account. When a cheat is detected, not only the account but also the hardware gets banned. HWID spoofers are used to bypass this.
Private cheats — harder to detect
Limited slots, unique builds, same-day updates. EAC doesn't know about software used by few.
Cheat catalog →Why Private Cheats Are Harder to Detect
Signature analysis runs on a knowledge base. To add a cheat to the database, EAC needs to get a sample — buy it, grab it from a leak, or receive it from a developer through a bounty program. A private cheat with a 30-50 slot limit has minimal leak risk.
Each copy of a private cheat can have a unique build — different obfuscator, different injection method, different variable names. Even if one copy reaches EAC, the signature won't match the rest.
Private cheat developers monitor EAC updates and adapt their code before new signatures go live. Public developers update too, but with a delay — and during that window thousands of users catch bans.
External vs Internal — The Safety Difference
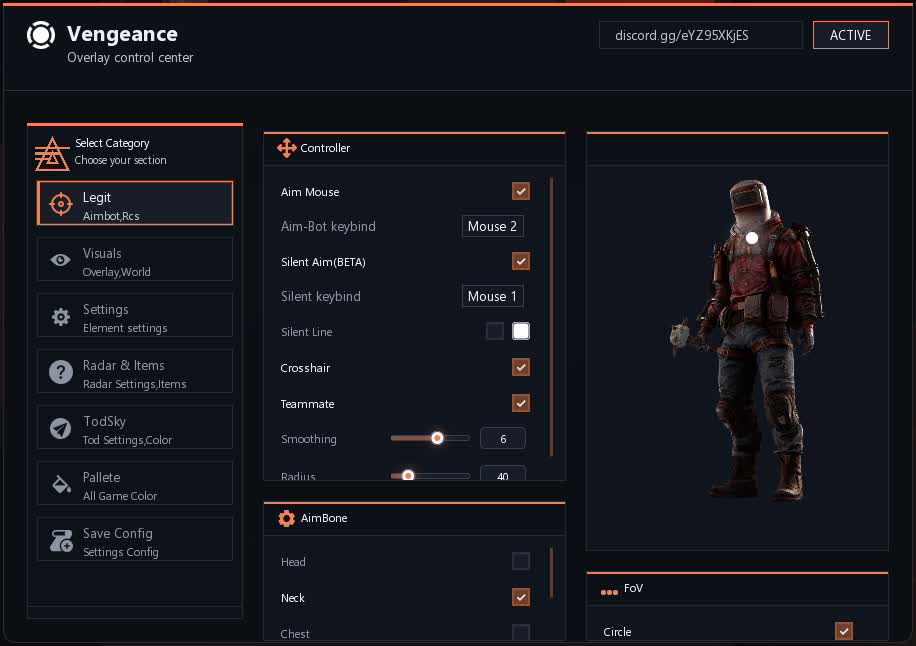
Internal cheats inject code directly into the Rust process. They get full access to game memory, which opens up features like PSilent (magic bullet) and Noclip. But injection is easier to detect — EAC scans loaded modules inside the process.
External cheats run in a separate process and read game memory through system calls. They leave no traces inside Rust but have limited functionality — some exploits are only possible through internal architecture.
From a safety standpoint, external cheats last longer. But internal product developers compensate with aggressive obfuscation and unique builds for each customer.
How to Stay Safe When Using Software
Play with an HWID spoofer — even if the cheat gets detected, they ban the spoofed identifier, not your real hardware. This is the single most effective precaution.
Pick private cheats with slot limits. The fewer people using the software, the lower the chance of it landing in EAC's signature database.
Don't use rage mode where other players can see you. Reports speed up manual review, and EAC's behavioral analysis factors in complaint frequency.
FAQ
What anti-cheat does Rust use?
Easy Anti-Cheat (EAC) from Epic Games. It runs at the operating system kernel level. Valve's VAC is not used in Rust.
Does EAC ban instantly or with a delay?
Bans can come hours or even days after detection. EAC collects data and processes it server-side rather than blocking in real time.
Can EAC be bypassed?
Yes, private cheats use obfuscation, unique builds, and injection methods that stay out of EAC's signature database. An HWID spoofer protects your hardware from a hardware ban.